I got one, and I really like it! This post will focus on just a few attributes of the new hardware that are salient to me.
Model Name: MacBook Pro
Model Identifier: MacBookPro10,1
Processor Name: Intel Core i7
Processor Speed: 2.7 GHz
Number of Processors: 1
Total Number of Cores: 4
L2 Cache (per Core): 256 KB
L3 Cache: 6 MB
Memory: 16 GB
Previous to this, my newest Mac is a top-end 2011 MacBookPro (the first vintage with thunderbolt), which I only mention because it’s crazy how much the hardware has changed in two years – even compared to a laptop with thunderbolt and SSD – beyond the expected ‘smaller / faster / cheaper’ improvements to components. I’ve only had a couple days with it so far, but here are some highlights of the differences:
- Retina. Amazing feature that also presents some amazing challenges.
- Additional thunderbolt port, which turns out to be the answer to
- No built-in ethernet or firewire
- No external case lights! None! Not a battery charge indicator, nor a system power indicator!
- Somebody clearly wanted the speakers to be badass.
- No optical drive (good riddance, imo – as long as you have one in the house somewhere)
Overall, it’s a fantastic upgrade, however there are a couple things that give me pause. I’m not really prepared to designate any of the negative-sounding items above as problems; they are tradeoffs, so the questions I ask are: Are these tradeoffs a good deal for me? Are they a good deal for an average user?
The first item of concern for me was the lack of built-in ethernet and firewire. I’m kind of a networking geek, so ethernet is important to me for a variety of reasons, even beyond the 900 Mb/s speed difference as compared to wifi:
- isolation of network traffic for troubleshooting / exploratory purposes
- remote attach via gdb (and possibly also support for uploading kernel core dumps)
- better security
- much better maximum density (there isn’t really that much wireless spectrum, while ethernet is only limited by the physical space occupied by the gear itself)
Of course most people probably don’t care much for the above, and I fully recognize that, which is why I’m now the owner of two shiny thunderbolt –> ethernet dongles, which are probably also the smallest ethernet NICs I’ve ever used. As far as I can tell, the entire ethernet feature set is supported – although I haven’t quite tried everything yet. One of the hardest parts (for me, not sane people) was figuring out good names for the dongles for use in static DHCP / DNS maps (since they each have a unique MAC address, and since they are highly interchangeable between hosts – granted, right now I only have one mac without built-in ethernet, but… ya know. Future-proof naming conventions are a thing ;)
Ok, so what do we gain in exchange for no ethernet / firewire, then? A case that is thinner than either of those connectors, which Apple achieved years ago starting with the MacBook Air. I think this is worth it, even for somebody like me who can enumerate reasons for wanting ethernet. The thunderbolt –> firewire dongle also seems fully functional. The additional flexibility of having either two ethernet ports or two firewire ports is also cool.
The tradeoffs for the no external case lights are perhaps not quite as obviously beneficial. Let’s start with the battery charge indicator. To me, battery charge level is useful information, and it is useful to be able to get that information with the lid closed – which is probably why Apple laptops have supported this for so long. As far as I can tell, this feature is gone for no gain other than the material benefit of omitting those parts, and perhaps simplifying the manufacturing and internal configuration by some (possibly significant) amount. Although a fairly minor issue, I’m putting this one in the sad-face column.
My internal jury is still out regarding the lack of a system power / activity light. Several times so far I have powered or rebooted the machine and waited through what seemed like a long POST, with *no* ability to tell if the system was on. I find this to be completely uncool, and even reasonably frustrating. What would I do differently with this information? Things that most users don’t do. I get that. The problem is, there is really no workaround, unlike with ethernet and firewire – and I’m completely serious in saying that I would buy a thunderbolt system power LED dongle, were it available. Not for regular use, but for when the shit has hit the fan. I really dislike the notion of removing useful information outlets, even if that information isn’t required all the time.
So what do we gain in exchange for no power / activity LED? As far as I can tell, the lines between system states are blurring, and there is the increasing possibility of transitions between states that might be ‘unwanted’ (i.e. noticeable == distracting) if the user knew they were happening (Power Nap for example), and it’s obvious to want to mitigate that potential annoyance. However, I still believe it would be a false choice between keeping the power indicator as-is, and annoying users with unattended state transitions. Why not change the LED behavior to not annoy or distract during Power Nap, but also still indicate system vitals when that knowledge is helpful? Other examples of when it’s helpful: maybe the system is asleep, and I want to shut down to save battery; or maybe I shut the lid but the system didn’t actually sleep (so now I need to find out why, and make it sleep). I realize both of these are things that users *shouldn’t* have to worry about, but I live in the world that exists, not the world that should exist, and these have both been part of my usage pattern for every laptop I’ve ever owned. Accordingly, lack of power / activity LED will probably go in the sad-face column, but I will allow time to determine the extent to which these issues are still present on this new hardware.
Regarding the retina display; the visual quality is amazing, and has given me a renewed appreciation for OS X UI aesthetics. I can really feel all the additional visual information and extra detail. So that’s the up side, and it’s hard to over-state this impact. Also interesting: the retina laptop hasn’t ruined the non-retina counterpart for me, like both the iPhone and iPad did.
Now, the other end of the tradeoff: I’m one of those people who is very sensitive to frame rate and animation performance. I had no illusions that retina resolutions would be as performant in all areas as compared to non-retina, on today’s GPUs. For the most part, performance is acceptably good for most common animations (scrolling, panning spaces), but some stuff animates slowly (resizing), and a few things animate very slowly (resizing with many sub-views). The increased drawing workload doesn’t really present any usability restrictions in day-to-day operation, but some workflows are notably impacted. For example, screen recording software now has a lot more work to do, and is usually resource-constrained even in non-retina resolutions. Initial screen recording test results are better than I expected, but there’s just no getting around all that extra work, and it will force me to change the way I do screen recordings (i.e. set the display resolution as low as possible; avoid heavy-handed animations).
Overall responsiveness feels notably improved compared to the 2011 MBP, in spite of occasionally slower drawing – probably due to the increased memory and CPU performance. SSD performance feels roughly the same. Raw CPU performance is moderately improved; here’s a quick encoding benchmark comparing these two laptops and my Mac Pro:
Source file: 1.4 GB QuickTime movie, 00:27, 1920 x 1200 @ 60 fps, ProRes 422
Re-encoded here using the avexporter sample code available from Apple
avexporter command used:
time avexporter -dest ~/t -replace -preset AVAssetExportPreset1920x1080 -source ~/Movies/wow.mov
Each config tested twice. Total elapsed wall-clock time for each test in bold. Lower numbers are better :)
# MacBookPro8,2 Intel Core i7 2820QM @ 2.3 Ghz / 32nm “Sandy Bridge” / Early 2011 (thor)
326.51s user 11.64s system 447% cpu 1:15.55 total
325.68s user 11.63s system 448% cpu 1:15.29 total
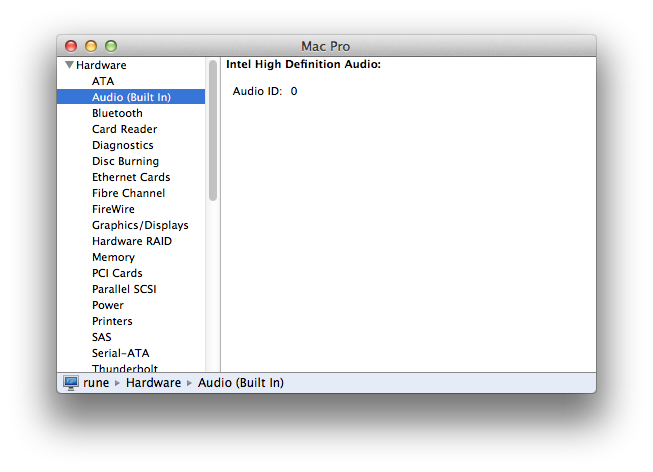
# MacPro4,1 Intel Quad Core Xeon W5590 @ 3.3 Ghz / 45nm “Nehalem” / Early 2009 (rune)
324.57s user 10.70s system 451% cpu 1:14.24 total
323.17s user 10.56s system 451% cpu 1:13.97 total
# MacBookPro10,1 Intel Core i7 3820QM @ 2.7 Ghz / 22nm “Ivy Bridge” / Early 2013 (foci)
270.30s user 10.58s system 446% cpu 1:02.97 total
269.87s user 10.47s system 445% cpu 1:02.95 total